Set Up OAuth Integration
Connect to external APIs with OAuth in 20 minutes
Instead of including a bunch of integrations, we give you the tools to build them by simplifying the difficult parts of building sustainable automation, including OAuth. In this section, you’ll setup a Microsoft Graph application as an OAuth provider and see how to use it in your automation.
What You’ll Build
Section titled “What You’ll Build”An OAuth connection to Microsoft Graph for reading user information.
Prerequisites
Section titled “Prerequisites”- Installation complete
- Administrator permissions to Entra ID
- Administrator permissions in Bifrost
Create Azure AD App Registration
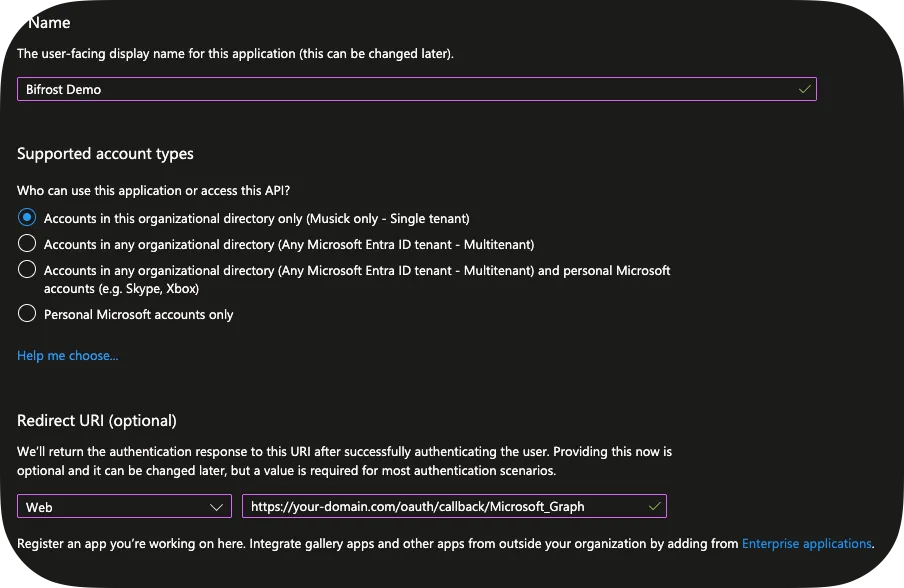
Section titled “Create Azure AD App Registration”-
Go to Entra ID → App registrations
-
Click + New registration:
- Name: “Bifrost Demo”
- Supported account type: Single Tenant
- Redirect URI:
https://your-domain.com/oauth/callback/Microsoft_Graph
-
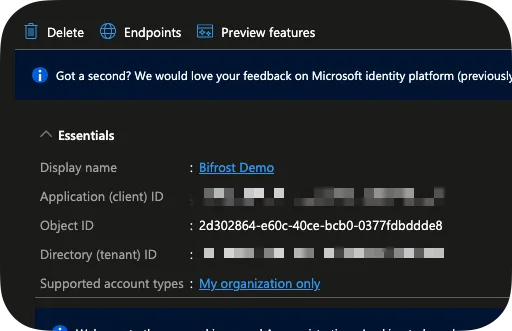
Copy Application (client) ID and Tenant ID
-
Click Endpoints and copy your
OAuth 2.0 authorization endpoint (v2)andOAuth 2.0 token endpoint (v2).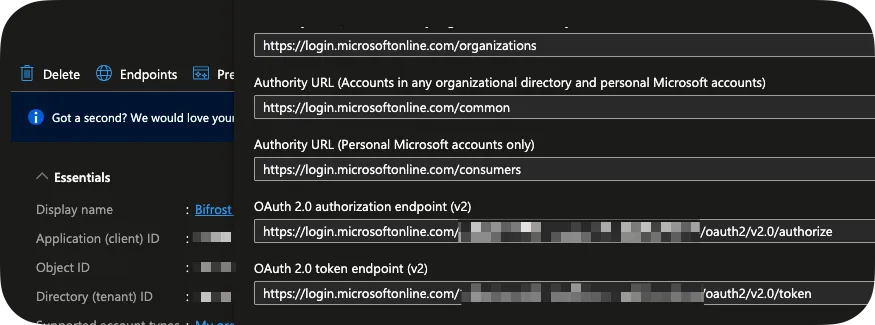
-
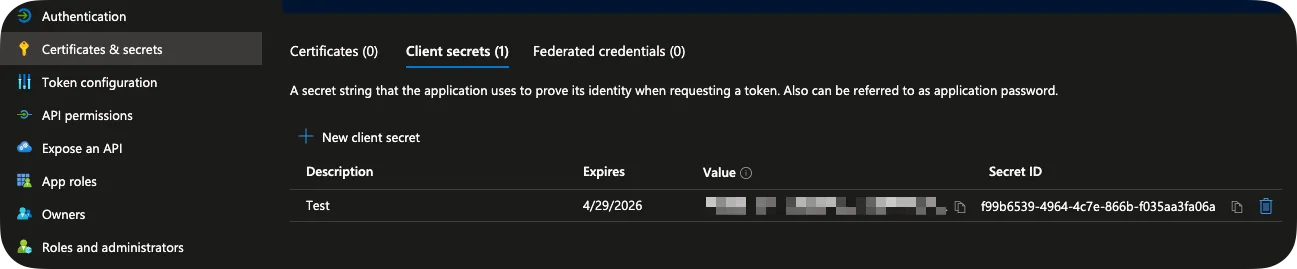
Go to Certificates & secrets → + New client secret:
- Set expiration to 6 months
- Copy secret value immediately
-
Go to API permissions:
- Click + Add permission → Microsoft Graph → Delegated
- Add
Directory.Read.All - Click Grant admin consent
Create OAuth Connection in Bifrost
Section titled “Create OAuth Connection in Bifrost”-
Navigate to Settings → Integrations → OAuth Connections
-
Click + Add Connection
-
Fill in details:
- Connection Name: Microsoft_Graph
- Description: My Microsoft Graph connection
-
Click Create
-
On
Custom Provider, fill in the following:-
OAuth Flow Type: Authorization Code (Interactive)
-
Client ID: The Client ID you copied earlier
-
Client Secret: The Client Secret you copied earlier
-
Authorization URL: The OAuth 2.0 authorization endpoint (v2) you copied earlier
-
Token URL: The OAuth 2.0 token endpoint (v2) you copied earlier
-
Scope: offline_access Directory.Read.All
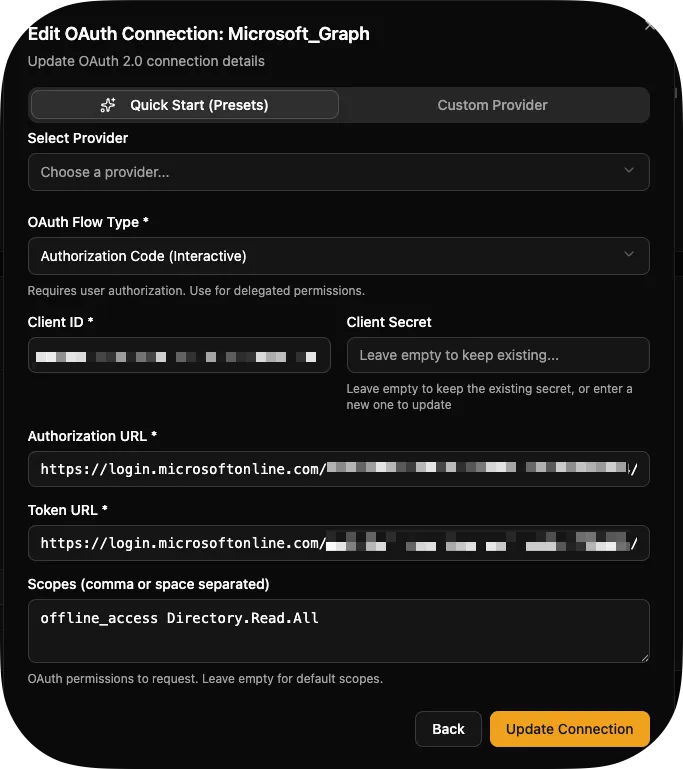
-
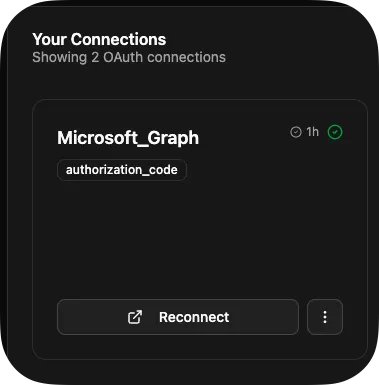
Authorize the Connection
Section titled “Authorize the Connection”-
Click Connect on your application
-
Sign in with Microsoft and consent to permissions
-
You’ll be redirected back to Bifrost
-
Connection status changes to Active
Use OAuth in Workflow
Section titled “Use OAuth in Workflow”-
In the Code Editor, create a new workflow called
list_users.pyfrom bifrost import workflow, param, oauth, ExecutionContextimport requestsimport loggingimport jsonlogger = logging.getLogger(__name__)@workflow(name="list_users",description="List users from Microsoft Graph")async def list_users(context: ExecutionContext):"""Fetch user information from Microsoft Graph."""# Get OAuth credentialsoauth_response = await oauth.get_token("Microsoft_Graph")logger.info("Retrieved oauth response")url = "https://graph.microsoft.com/v1.0/users"headers = {"Authorization": f"Bearer {oauth_response['access_token']}"}response = requests.get(url, headers=headers)response.raise_for_status()users = response.json()['value']return users -
Use
CTRL/CMD + Sto save. -
On the Workflows screen, click Execute Workflow on your
list_usersworkflow.
Token Refresh
Section titled “Token Refresh”Bifrost automatically refreshes expired tokens provided your connection returned a refresh token. It’ll tell you if it doesn’t. If the connection is unable to refresh for some reason — such as the password on the account you used to authenticate becoming invalid — you’ll see the error on the OAUTH Connections screen.
Multiple Organizations
Section titled “Multiple Organizations”OAuth connections are organization-scoped:
-
Each org can have its own
microsoft-graphconnection -
Workflows automatically use the executing org’s credentials or fall back on the global connection, but you can specify something else if you want like this:
await oauth.get_token("Microsoft_Graph", 'some-other-org-id') -
No code changes needed for multi-tenancy!
Next Steps
Section titled “Next Steps”- OAuth Setup Guide - Advanced OAuth patterns
- Secrets Management - Secure credential storage
- Microsoft Graph Guide - Common Graph API patterns